Portal26 Elasticsearch Security
How can I secure my data inside Elasticsearch?
Learn how Portal26 locks down Elasticsearch data with encryption-in-use

How can I secure my data inside Elasticsearch?
Learn how Portal26 locks down Elasticsearch data with encryption-in-use
Securing data inside Elasticsearch is crucial to prevent cyberattacks, unauthorized access, and data breaches, which can lead to severe consequences such as financial losses and reputational damage. However, Implementing strong security measures such as NIST FIPS 140-2 certified searchable encryption can significantly reduce the risk of these incidents and ensure that your data remains protected.
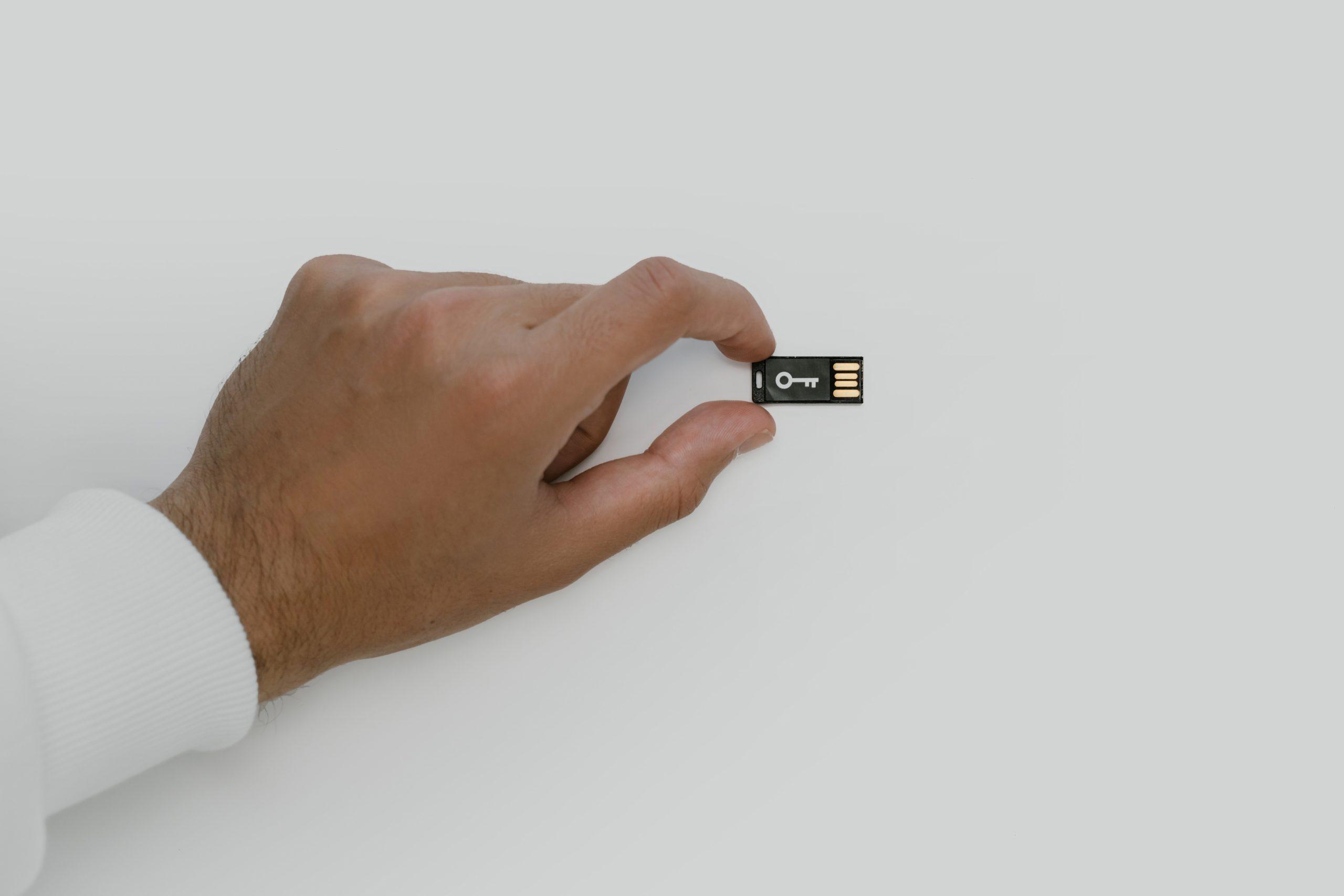
Securing Elasticsearch with Portal26 Plugin
Conducting search and analytics on vast quantities of data requires the indexing and persisting of this data in clear text inside enterprise search platforms such as Elasticsearch. These platforms are the perfect targets for data hungry ransomware and extortion actors, who either look for misconfigured clusters or steal admin credentials.
Portal26 is finally here to put an end to all that by offering advanced Elasticsearch searchable encryption technology.
Here is how we use encryption-in-use or searchable encryption to neutralize all such attacks.
Enable Security in Elasticsearch - Portal26 Plugin Features

Explore How Our Elasticsearch Security Plugin Keeps Enterprise Search Data Secure From Attacks And Exposure
How it Works
Watch a Demo
Elasticsearch is a trademark of Elasticsearch BV, registered in the U.S. and in other countries.